✅ The Ultimate Cheat Sheet for Android and iOS hacking: Part I (Static Analysis)
Learn how to analyze and bypass security for APK and IPA files.
Learn how to analyze and bypass security for APK and IPA files.
Frameworks
APKInspector
APKinspector is a powerful GUI tool for analysts to analyze the Android applications.
APKTool
Tool for reverse engineering 3rd party, closed, binary Android apps. It can decode resources to nearly original form and rebuild them after making some modifications.
To decompile:
apktool d package.apkTo build after the modifications:
apktool b packageReferences:
Sign an apk
Recompile APK:
apktool b decompiled/apk/directory -o app-patched.apkZipalign APK to make it compatible with Android:
zipalign -p 4 app-patched.apk app-aligned.apkSign APK with Android debug key (Password: android):
apksigner sign --ks ~/.android/debug.keystore app-aligned.apkIf you don’t have Android Studio installed, use those commands instead, to sign the apk:
Create a signing key:
keytool -genkey -v -keystore my-release-key.jks -keyalg RSA -keysize 2048 -validity 10000 -alias my-aliasSign the APK:
apksigner sign --ks my-release-key.jks app-aligned.apkVerify signature
Validate an APK signature
apksigner verify -v --print-certs name.apkAndroguard
Androguard is a full python tool to play with Android files.
For decoding Android XML (AXML):
androguard axml res/xml/network_security_config.xmlFor decoding resources.arsc:
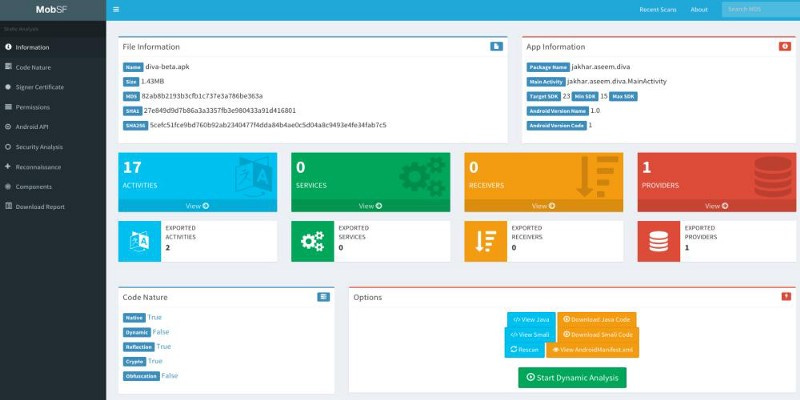
androguard arsc resources.arscMobile Security Framework — MobSF
Mobile Security Framework is an intelligent, all-in-one open source mobile application (Android/iOS) automated pen-testing framework capable of performing static and dynamic analysis.
git clone https://github.com/MobSF/Mobile-Security-Framework-MobSF.git
cd Mobile-Security-Framework-MobSF
pip install -r requirements.txt
python manage.py runserveror using Docker:
docker pull opensecurity/mobile-security-framework-mobsf
docker run -it -p 8000:8000 opensecurity/mobile-security-framework-mobsf:latest
firefox http://localhost:8000Reverse Engineering
.smali reverse engineering tools
baksmali
smali
Steps:
Unzip
unzip test.apk2. Baksmali
baksmali classes.dex -o smaliClasses3. Smali
smali smaliClasses -o classes.dex4. Zip -r
zip -r test.apk AndroidManifest.xml classes.dex res/ resources.arsc5. Jarsign
java -jar signapk.jar testkey.x509.pem testkey.pk8 test.apk test-patched.apk6. Zipalign
zipalign -v 4 test-patched.apk final-apk.apkHow to transform an aab (Android Bundle) to apk
First, download https://github.com/google/bundletool/releases
java -jar bundletool.jar build-apks --bundle=name.aab --output=name.apks
mv name.apks name.zip
unzip name.zip -d nameAndroid apk reverse engineering
Unziping the APK, we can convert all Dalvik dex files to a jar file:
d2j-dex2jar -f classes.dexDirectly from the jar file we can decompile it to get the source code:
java -jar jd-gui/build/install/jd-gui-osx/JD-GUI.app/Contents/Resources/Java/jd-gui-1.4.0.jar $FILE.jarAndroid:allowBackup
curl https://github.com/nelenkov/android-backup-extractor/releases/download/20181012025725-d750899/abe-all.jar -o abe.jar
adb backup -apk -f out.ab $PACKAGE
java -jar abe.jar unpack out.ab out.tar
tar xvf out.tarReferences:
Unity Engine Reverse Engineering from Windows
Download https://github.com/Perfare/Il2CppDumper (Unity il2cpp reverse engineer)
apktool d package.apkcopy package\lib\armeabi-v7a\libil2cpp.so .copy package\assets\bin\Data\Managed\Metadata\global-metadata.dat .Il2cppDumper.exe libil2cpp.so global-metadata.dat package_re\Now open package_re\DummyDll\Assembly-CSharp.dll with DnSpy
Also you can use the following Frida wrapper to save time: https://github.com/vfsfitvnm/frida-il2cpp-bridge
iOS Reverse Engineering
To reverse engineer IPA files use Hopper: https://www.hopperapp.com/ (Hopper Disassembler, the reverse engineering tool that lets you disassemble, decompile and debug your applications).
Or Veracode iRET framework: https://www.veracode.com/blog/2014/03/introducing-the-ios-reverse-engineering-toolkit
Disassembling OPcodes
Best option is to use http://shell-storm.org/online/Online-Assembler-and-Disassembler/
And https://armconverter.com/?code=nop
Also Google’s Dalvik bytecode page is a good resource.
AndroidManifest.xml Analysis
You can always exclude a task from the Recents screen entirely by setting the <activity> attribute, android:excludeFromRecents to true.
Source: https://developer.android.com/guide/components/activities/recents
Other useful resources inside the apk file:
res/values/strings.xml
You will also like the second series of this topic: